classified
-

War Plan Chat Includes Journalist
Journalists aren’t usually invited to online chats about US war plans. This seemed obvious until yesterday,…
-

Leaking Secrets Under Social Pressure
Here is a classic example of human nature: people on a gaming site argue that the…
-

SCI//HCS-P/SI/TK at Mar-a-Lago
This is a brief explanation of the weird acronyms on the cover sheets that appeared in…
-

The Mar-a-Lago Mess
Update: Former President Trump has been indicted under federal laws for unlawfully retaining government documents and…
-
Telepathic Declassification
Former President Trump recently suggested that the sitting President simply needs to “think” something is declassified…
-
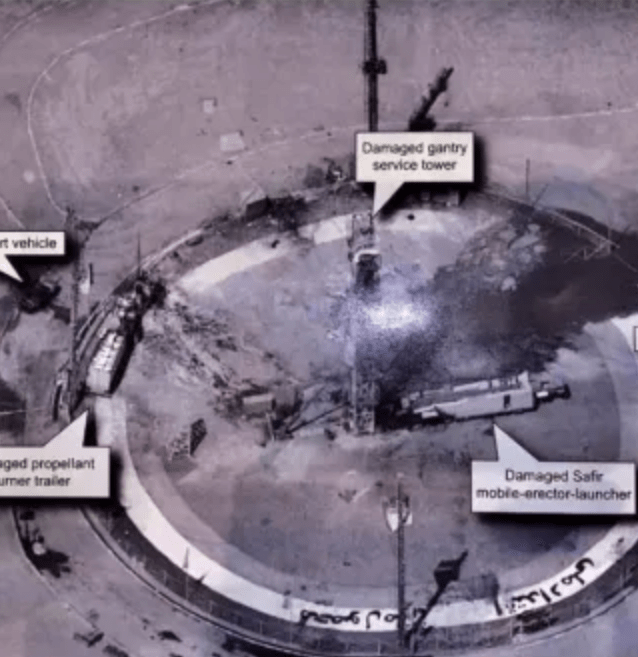
Update: Tweeting Top Secret
Back in the dark ages of the Trump presidency, the President tweeted this photograph. An earlier…
-

“Eyes Only” Revisited
I was poking around declassified documents from the National Reconnaissance Office (NRO) and found a reference…
-
“Eyes Only” Security Marking
[This post has been UPDATED three times since first published, most recently on Nov 14, 2019]…
-
Comparing Leaks: Trump vs. Hillary
As I said in an earlier post, no crime is committed if the appropriate official leaks…
-
A Yank at Bletchley Park
A friend and colleague introduced me to a 94-year-old gentleman with a rare tale to tell. John…
-
NSA re-releases Boak’s Lectures
I’m a fan of Boak’s Lectures – they cover the fundamentals of military cryptography just before…
-
Clinton’s Email Server Isn’t Her Scandal
Early last month, Edward Snowden criticized former Secretary of State Hillary Clinton for obviously and intentionally mishandling classified…
-

Security Design Principles
This is an extended, less-edited version of an article appearing in IEEE Security and Privacy in December 2012. This…
-
Boak’s Puzzle: Disposing of Classified Trash
Recently I was skimming through the NSA’s “classified history of COMSEC” (Volume 1 and Volume 2). This…

You must be logged in to post a comment.