authentication
-
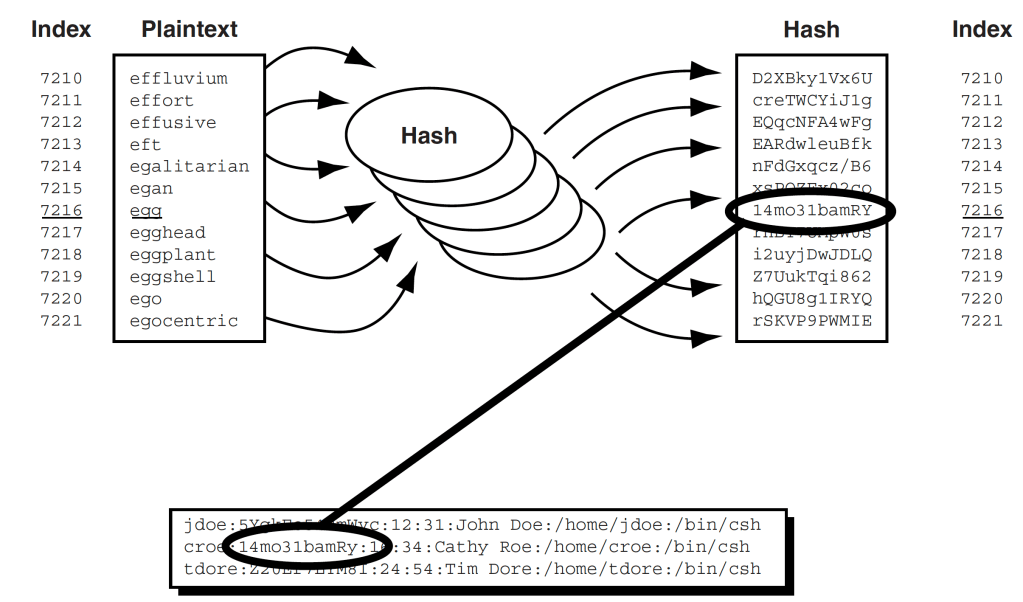
Basic Tech-y Article on Password Hacking
Here’s an article from last year’s Scientific American: The Mathematics of (Hacking) Passwords. If you remember…
-
Authentication Chapters Online
Thanks to my former publisher, Addison-Wesley nee-Pearson Education, I can post several chapters of my favorite…
-
Political campaign security
Maciej Cegłowski has published a long, practical, insightful, and witty article on his experiences with political…
-
Design Patterns for Identity Systems
These are design patterns in the Christopher Alexander sense rather than the object oriented design sense:…
