I have posted the fifteenth video in the Cryptosmith Series on practical basic cryptography.
These videos use animation to explain basic crypto techniques. More people need to understand crypto technology. We all rely more and more on mobile and Internet security mechanisms. Aside from protecting online commerce and financial activities, many professionals are realizing that their daily activities require strong protection.
The video collection has three parts:
Here are PDFs built from the animated slide decks:
- 1 Network Crypto – Cryptosmith videos 1-5
- 2 DVD Embedded Crypto – Cryptosmith videos 6-9
- 3 Public-Key Certificates – Cryptosmith videos 10-15
Network Crypto
- Video 1: Introduction to the series
- Video 2: Eavesdropping and encryption
- Video 3: Secret sharing and public-key crypto
- Video 4: SSL/TLS Transport Layer Security
- Video 5: Protecting message integrity
- Video 10 (out of order!): Old-school SSL/TLS with the RSA cipher
DVD Embedded Crypto
- Video 6: Examples of weak crypto in DVDs
- Video 7: Key wrapping and least privilege in DVDs
- Video 8: Playing a DVD – how it works
- Video 9: Publishing a DVD – how it works
Public-Key Certificates
- Video 11: Identifying Internet servers with public-key certificates
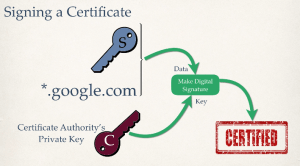
- Video 12: Digital signatures
- Video 13: Validating a public-key certificate
- Video 14: Who signs a public-key certificate
- Video 15: Delegation and certificate chaining
Production Notes
I used Apple’s Keynote, their PowerPoint clone. I’m not sure why I didn’t use PowerPoint except that I’d used Keynote earlier for videos. Now I’m used to it.
I export videos in 1080p. Vimeo complains about this, because the resulting videos don’t have the bitrate of life motion video, and they think I’ve broken the videos somehow.
I have a Blue Yeti microphone that I use in cardioid mode. It works really well except when the dog barks. I don’t use a wind or pop screen. The gain setting is at the halfway point. I tried different gain settings but had inferior results.

Responses
[…] See the latest post to summarize the video […]
LikeLike
[…] I have posted the fifteenth video in the Cryptosmith Series on practical basic cryptography. The video collection falls into three parts: the network crypto introduction, the DVD example, and the public-key certificate discussion. There are also updates to other series videos. They now use the acronym “SSL” a lot more, since people recognize it more often than “TLS.” … Continue reading Cryptosmith Video Series #1 through #15 → […]
LikeLike