Tech Teaching
-

Teaching with Design Principles
Design principles help students learn the essentials of technical design tasks. Students apply simple-sounding rules to…
-

GPT and Confirmation Bias
“Garbage in, garbage out.” In computing we’ve recited the GIGO motto since I was in diapers…
-

Cybersecurity for MSSE 2023
MSSE second-year students may request a cybersecurity elective as course SENG 5271. If the course is…
-
Online Course: Cloud Top Ten Risks
I am pleased to report that the fourth course for the University of Minnesota in my…
-

Cybersecurity for MSSE 2022
I am offering an online cybersecurity elective to MSSE second-year students for 2022: SENG 5271. It…
-
Cloud Security Specialization Launched
The University of Minnesota now offers a Cloud Security specialization through Coursera. It contains four courses…
-
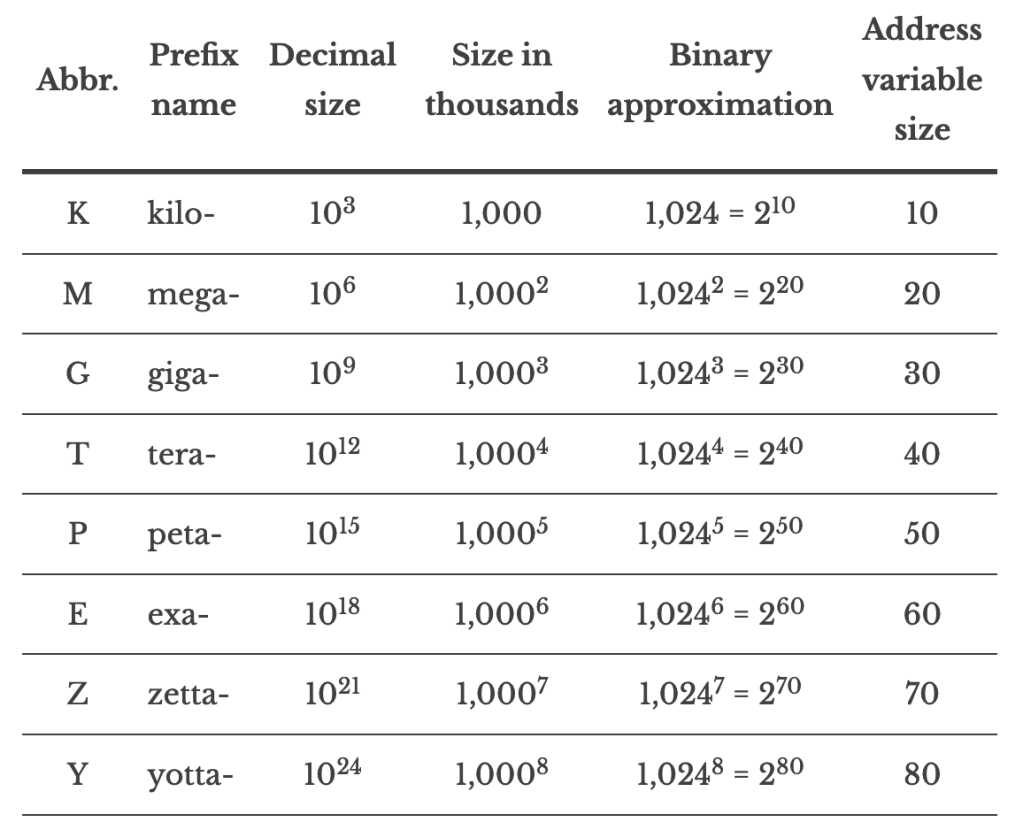
Memory Sizes: Now with zetta and yotta!
One of the most popular pages on this site provides a simple conversion to map numbers…
-

2021 MSSE Cloud Security Elective
UPDATE: This elective will be offered to second-year MSSE students at the University of Minnesota as…
-

Solo Studio for Video Lectures
I’ve been recording video lectures for a Coursera specialization in cloud computing. The first of the…
-
FCPX and the Solo Studio
In other posts I describe how I’m producing videos for a Coursera specialization. This is a…
-
Online Course in Cloud Security Basics
I now offer an online course on Cloud Security Basics under the auspices of the University…
-
WPA2 Packet Frame Format
Wireless Protected Access, Version 2 (WPA2) is the version of Wi-Fi security used in most cases…
-
Organizing Video Clips for an Online Course
I’ve signed on to do a Coursera online course on cloud security. I’ll share more details as…
-
Cryptosmith Video Series
I have posted the fifteenth video in the Cryptosmith Series on practical basic cryptography. These videos use animation…
-
MSSE Cybersecurity Course 2017
Members of the University of Minnesota’s MSSE Class of 2017: the cybersecurity course (titled “Data and Network…
-
Adieu, Online School
I have shut down my online school. It was an interesting experience, but not a cost-effective…
-
Reviewer Links for Cloud Computing
Thank you for reviewing Cloud Computing videos! I’m posting draft videos on my Vimeo site. Here…
-
Streamlined NSTISSI 4011 Training Certificate
Cryptosmith Institute now offers a second option for earning an NSTISSI 4011 training certificate: The original option:…
-
MSSE Cybersecurity Elective 2016
I am offering a Cybersecurity elective for students registered in the University of Minnesota’s Master of Science…
-
Digital’s RT-11 File System
(Circa 1975-199?) The PDP-11 computer, build by Digital Equipment Corporation (DEC) in the late 20th century,…
-
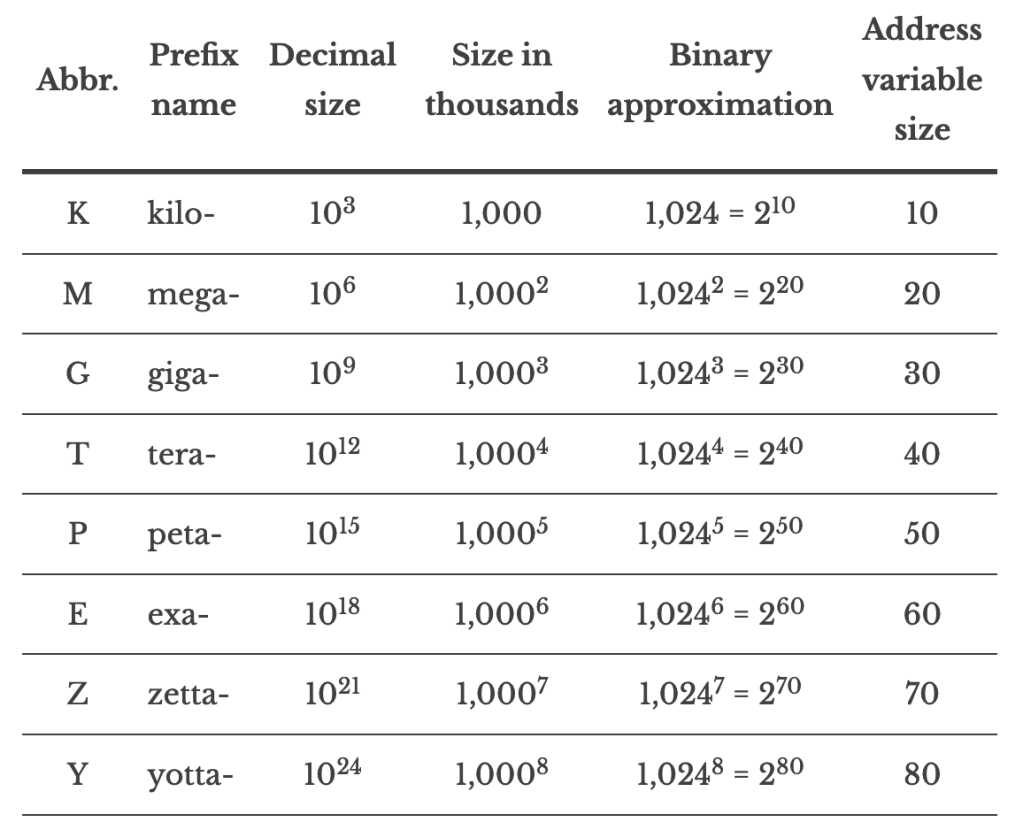
Kilo mega giga tera
I am not keeping this page up to date. Please visit https://cryptosmith.com/2013/10/18/memory-sizes-kilo-mega-giga-tera-peta-exa/ instead. Here is a…
-
Memory Sizes: kilo mega giga tera peta exa
Here is a table summarizing large numbers, their names, and the number of bits they require…
-
Boston University’s RAX Library
(circa 1973-8) Boston University (BU) developed its own timesharing system in the 1970s for its IBM 360…


You must be logged in to post a comment.