Security
-
Why Signalgate Matters
I found this in my files. I no doubt intended to publish it months ago and…
-

Another Telephone Phish
A person called me on the phone a few moments ago claiming to be from US…
-
Making Fun of Quantum Codebreaking
Quantum codebreaking uses a theoretically “large” quantum computer to break secret codes. Today, quantum computers handle…
-

War Plan Chat Includes Journalist
Journalists aren’t usually invited to online chats about US war plans. This seemed obvious until yesterday,…
-
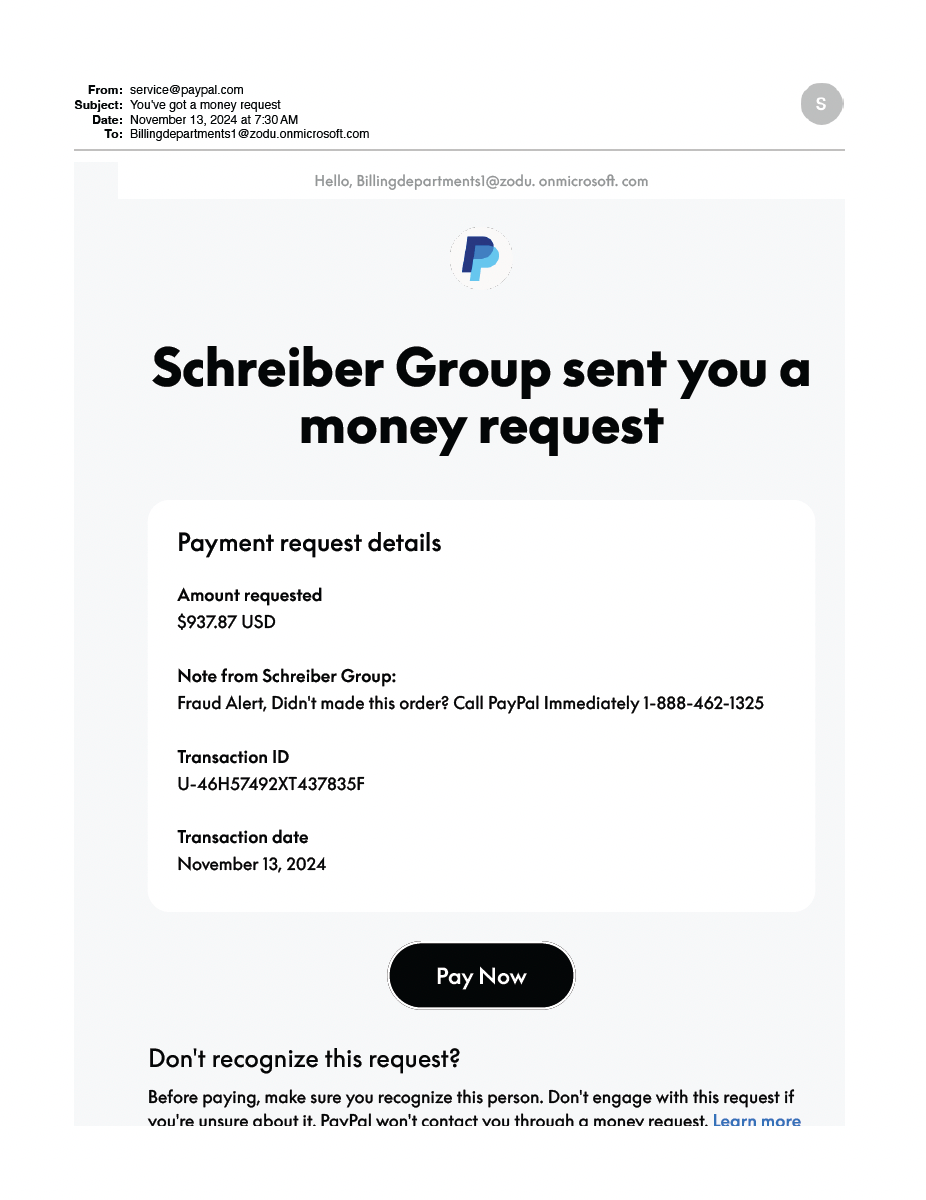
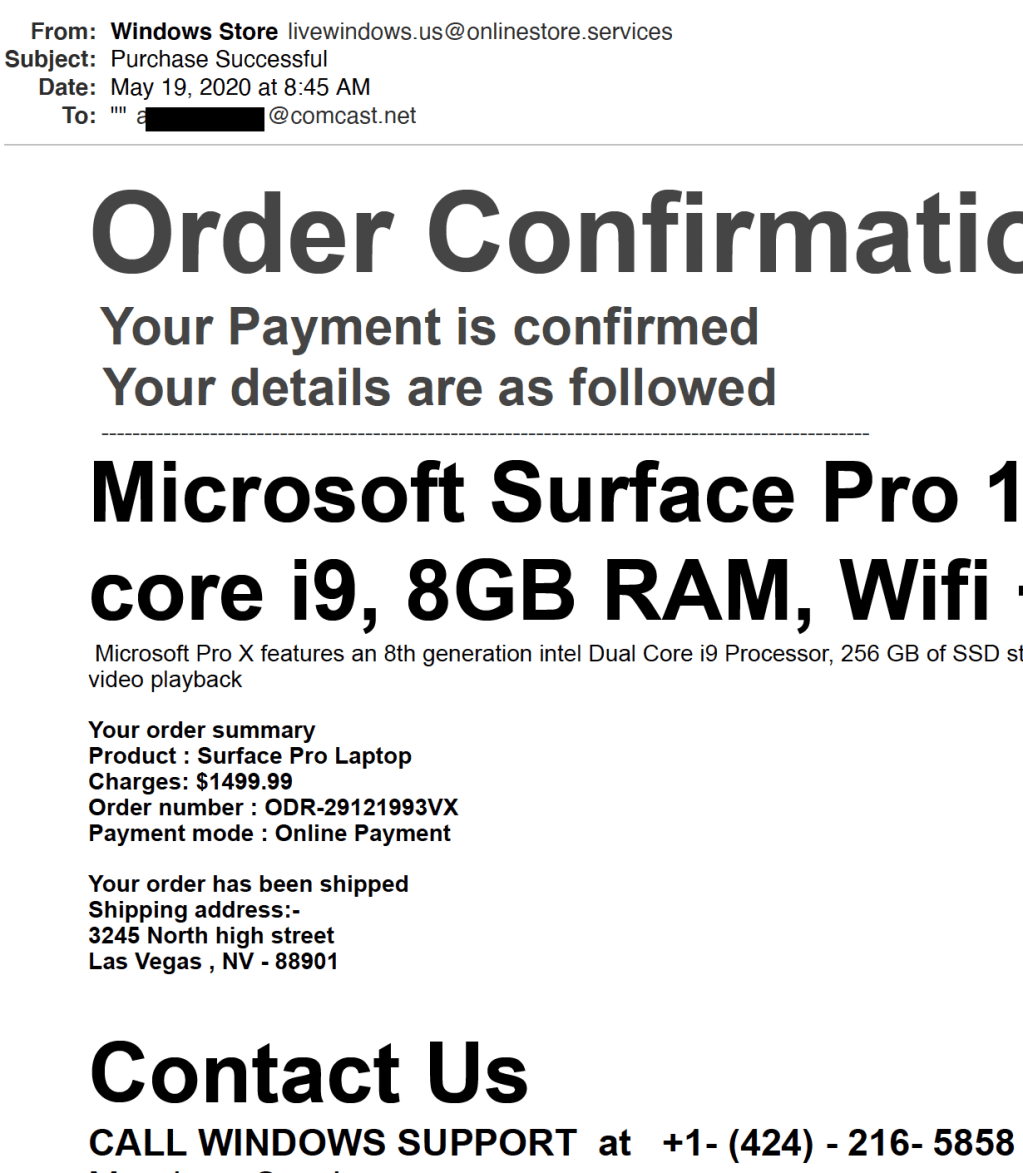
Clever PayPal-based Attack
Do not call that number! This attack is brilliant. It uses a legitimate PayPal email message…
-

Breaking Bitlocker
It was only a matter of time before someone did this. Bitlocker is Microsoft’s technique for…
-

Play the Password Game!
A clever person has hosted a Password Game. Give it a try!
-

Leaking Secrets Under Social Pressure
Here is a classic example of human nature: people on a gaming site argue that the…
-

SCI//HCS-P/SI/TK at Mar-a-Lago
This is a brief explanation of the weird acronyms on the cover sheets that appeared in…
-

The Mar-a-Lago Mess
Update: Former President Trump has been indicted under federal laws for unlawfully retaining government documents and…
-
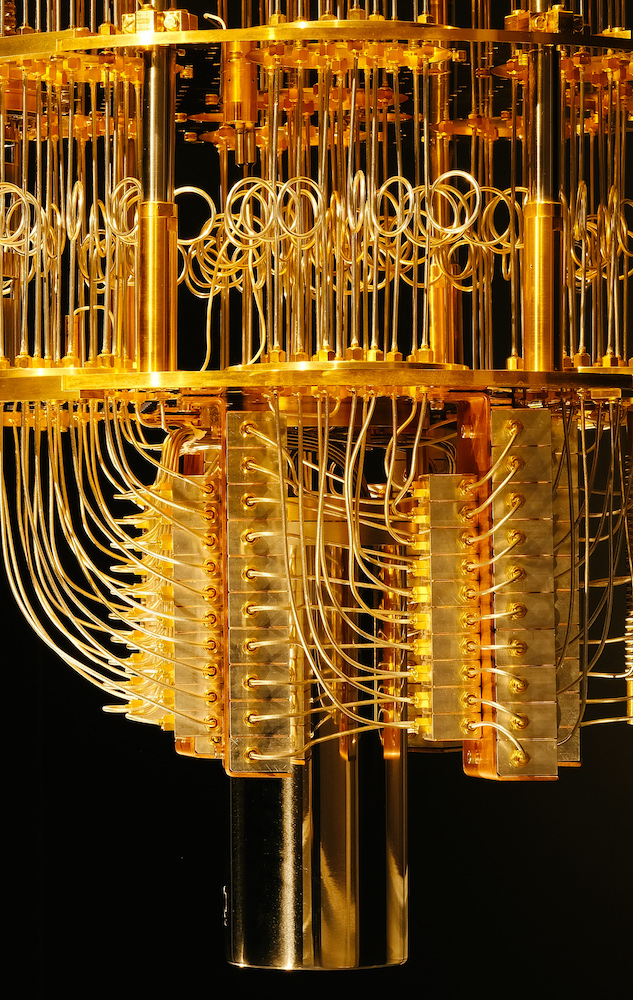
The Quantum Computer Bogeyman
Peter Gutmann of the University of Aukland recently published a parable “On the Heffalump Threat.” He…
-
Telepathic Declassification
Former President Trump recently suggested that the sitting President simply needs to “think” something is declassified…
-

Email Attack via a Recycled Domain
A software engineering friend fell victim to an almost-successful attack on his Facebook account. The attacker…
-
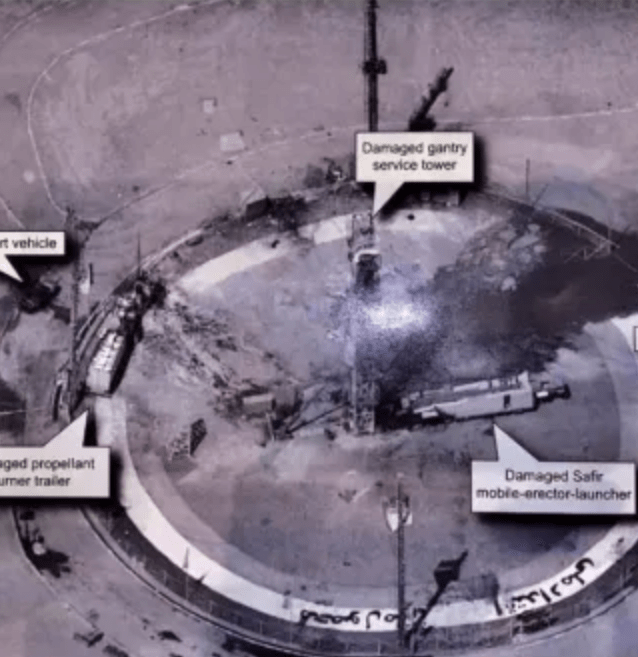
Update: Tweeting Top Secret
Back in the dark ages of the Trump presidency, the President tweeted this photograph. An earlier…
-

Cities, Disneyland, and Software Security
I like to think of our modern software infrastructure as being like a large city and…
-

libhairshirt vs libfootgun
Peter Gutmann, an interesting crypto-academic from New Zealand, has proposed discussing two crypto libraries, libhairshirt and…
-
Selling It: Crypto Edition
Here is a crypto version of “Selling It,” a long-running back-page column in the magazine Consumer…
-

Old Story: Leaked Voter Records
My previous posting on the Proud Boys spam email speculated that voter records were widely available…
-

“Proud Boys” Emails Are Bogus
The Proud Boys emails aren’t actual threats. They’re the lowest form of anonymous spam.
-

Krebs’ Three Rules
Like most people, I’m drawn to those small lists of “rules” that promise to make our…
-
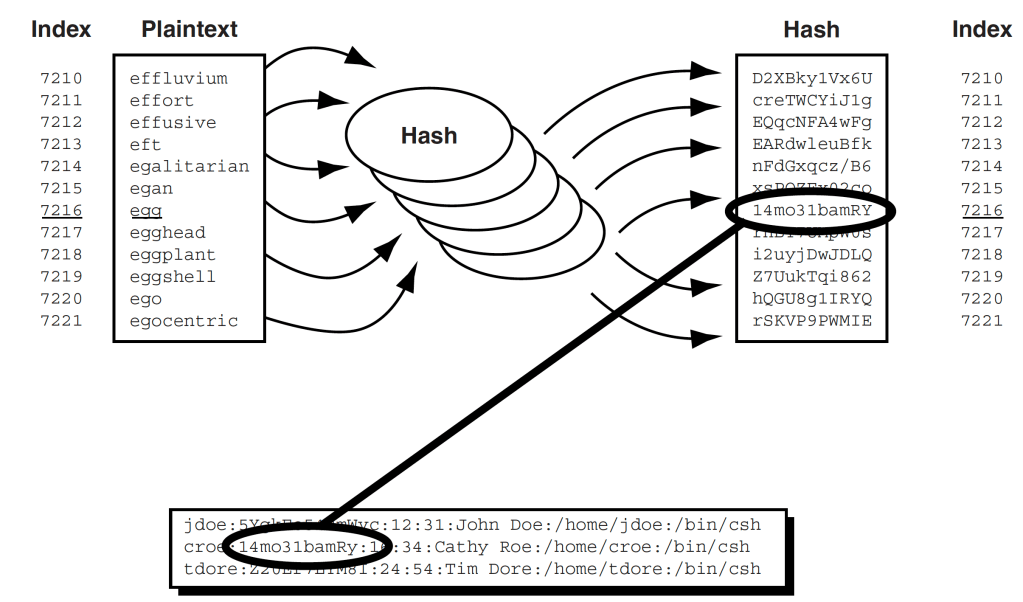
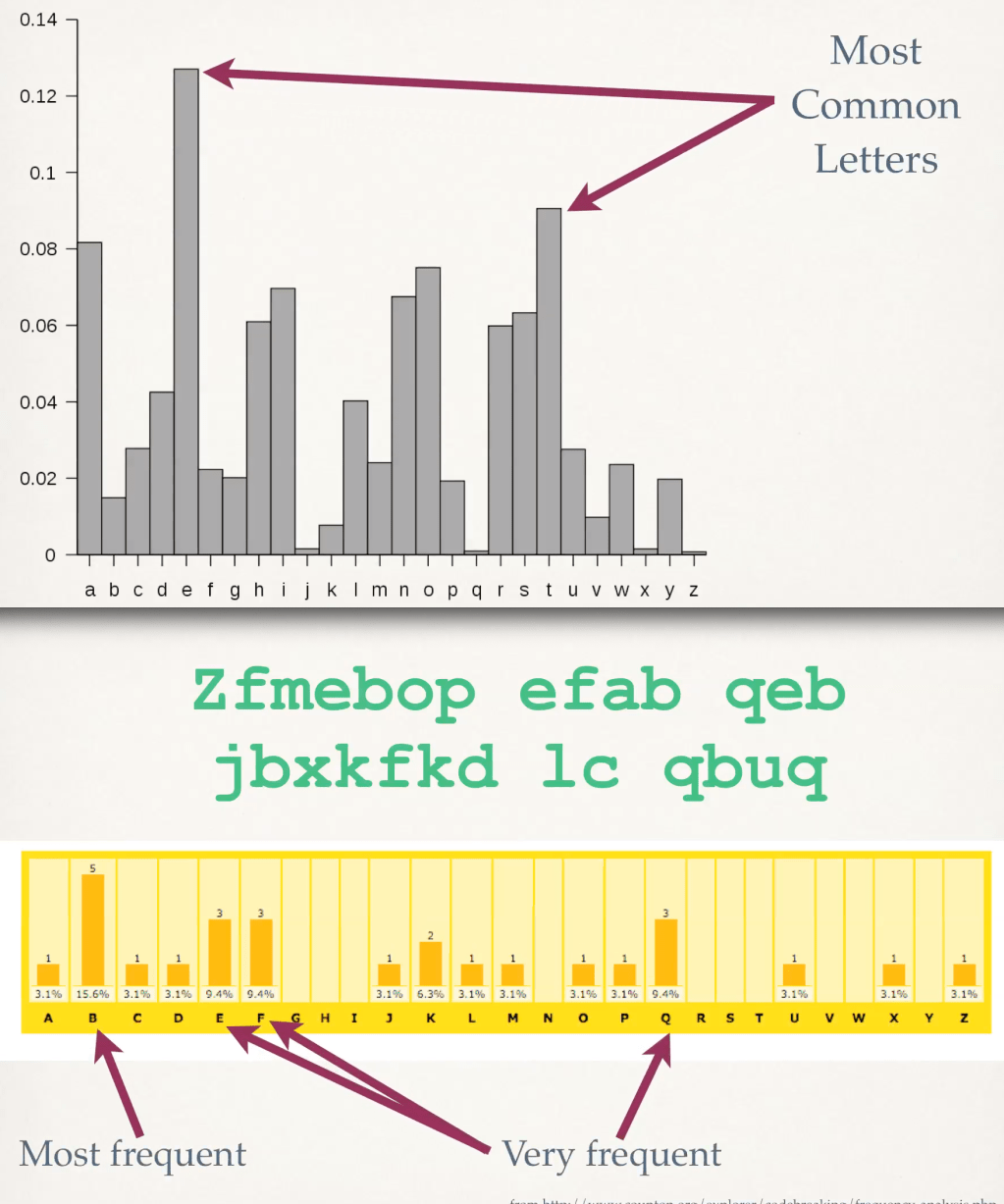
Basic Tech-y Article on Password Hacking
Here’s an article from last year’s Scientific American: The Mathematics of (Hacking) Passwords. If you remember…
-

Assessing an Email’s Legitimacy
I recently received an email sporting “Wells Fargo” logos. It asked me to do a survey.…
-
Beware of Phone Phishing
Just because the email (or letter) directs you to a phone number doesn’t mean you aren’t…
-

“Eyes Only” Revisited
I was poking around declassified documents from the National Reconnaissance Office (NRO) and found a reference…
