Favorite Posts
Memory Sizes: kilo mega giga tera peta exaOctober 18, 2013
SCI//HCS-P/SI/TK at Mar-a-LagoJune 4, 2023
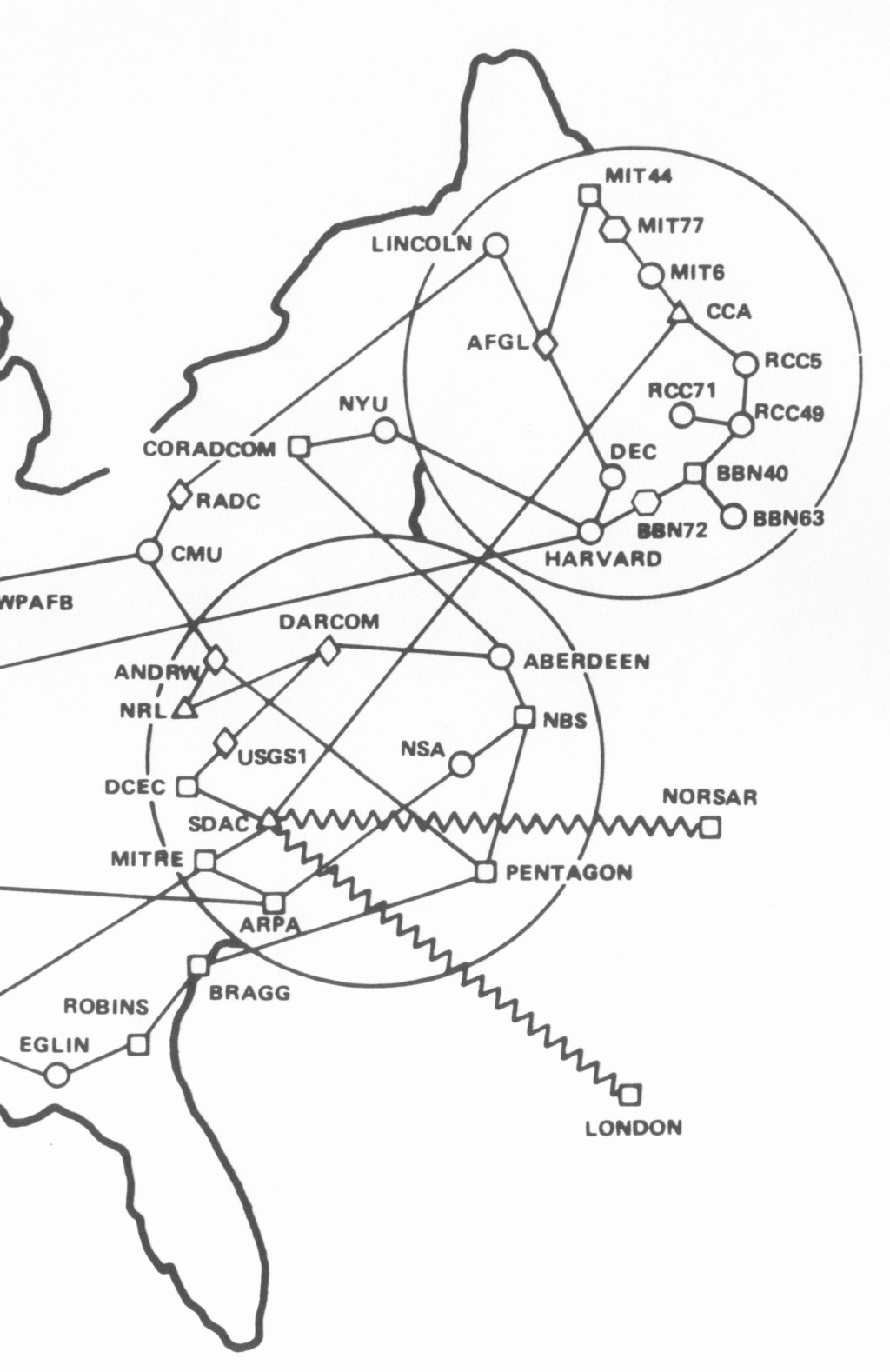
ARPANET MapsApril 29, 2024
Kilo mega giga teraOctober 19, 2013
Security Design PrinciplesOctober 19, 2013
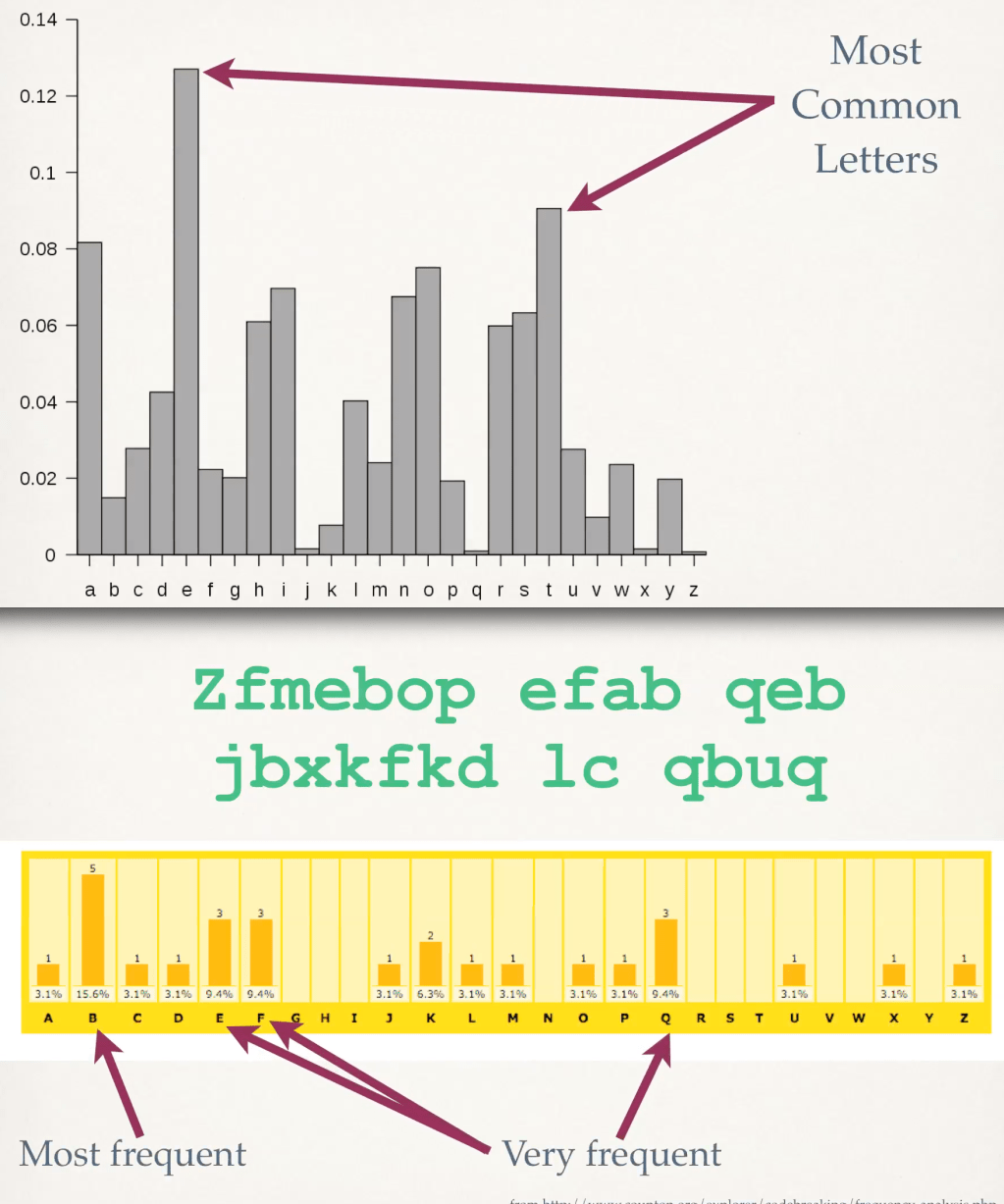
Stream Cipher Reuse: A Graphic ExampleMay 31, 2008
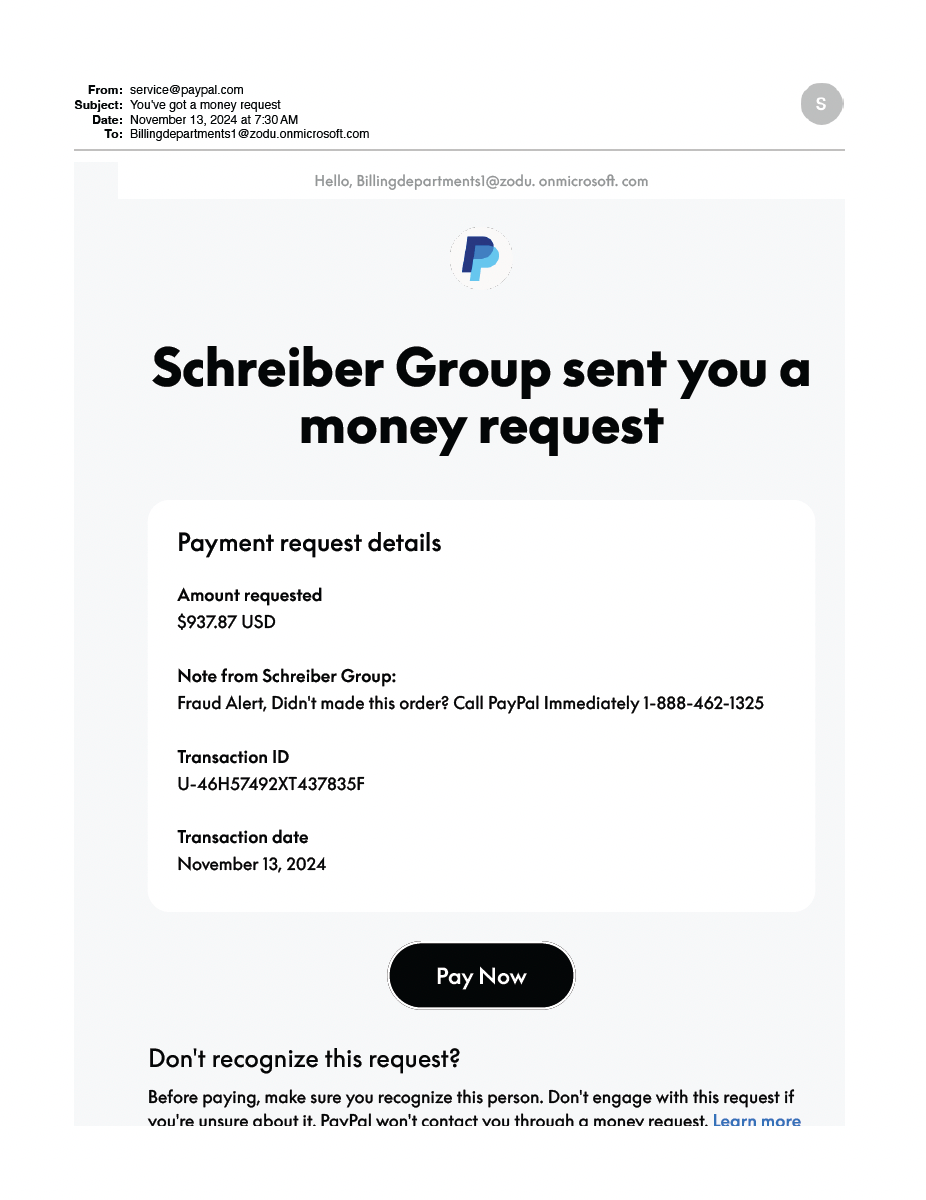
ACSAC Android Apple attacks authentication Boak Calibre certificates CIA properties classified Clinton cloud computing Coursera CPU cracking crypto databases DEC design principles domain names Drupal ebooks elections email encrypted messages evaluations file systems flaws Ft. Meade GUI history iOS iPhone KGB Kindle library memory sizes Microsoft mobile security MSSE Multics NSA NSTISSI 4011 OPDS passwords PDP-11 phishing President quantum Quizlet RAM risks RT-11 secrecy spam SSL stream cipher TCSEC Top Secret training Trump UMN video Wordpress xor