Security
-

Self-teaching a little security thinking
There’s a particular mindset we call security thinking. I’ve also seen it called ‘reasoned paranoia.’ The…
-
Detecting a Phish on an iPhone
In their obsession with simplifying the phone interface, the iPhone designers make it a bit harder…
-
Life Cycle of a Security Bug
Unlike members of the insect family, computer software bugs live forever. Software security bugs (well, flaws)…
-
“Eyes Only” Security Marking
[This post has been UPDATED three times since first published, most recently on Nov 14, 2019]…
-
Authentication Chapters Online
Thanks to my former publisher, Addison-Wesley nee-Pearson Education, I can post several chapters of my favorite…
-
Political campaign security
Maciej Cegłowski has published a long, practical, insightful, and witty article on his experiences with political…
-
Ross Anderson and another edition of Security Engineering
Every cybersecurity professional knows – and almost certainly owns – this book. Ross Anderson published the…
-
A Forged “From” Address
To the left we see part of a malicious email. The author brags about how the…
-
Rule #1 for Detecting a Phish
Golly. This one was really hard to spot. Just kidding. This is obviously a fake email.…
-
A Mac Hack
Here’s a clever two-step attack on a Macintosh. First, the victim downloads a file – it…
-
Invoice Phishing Campaign
Here is a phishing email I received today. These almost always land in my junk mail…
-
State of the Art Password Cracking
While researching my next edition of Elementary Information Security I came a this posting from last January.…
-
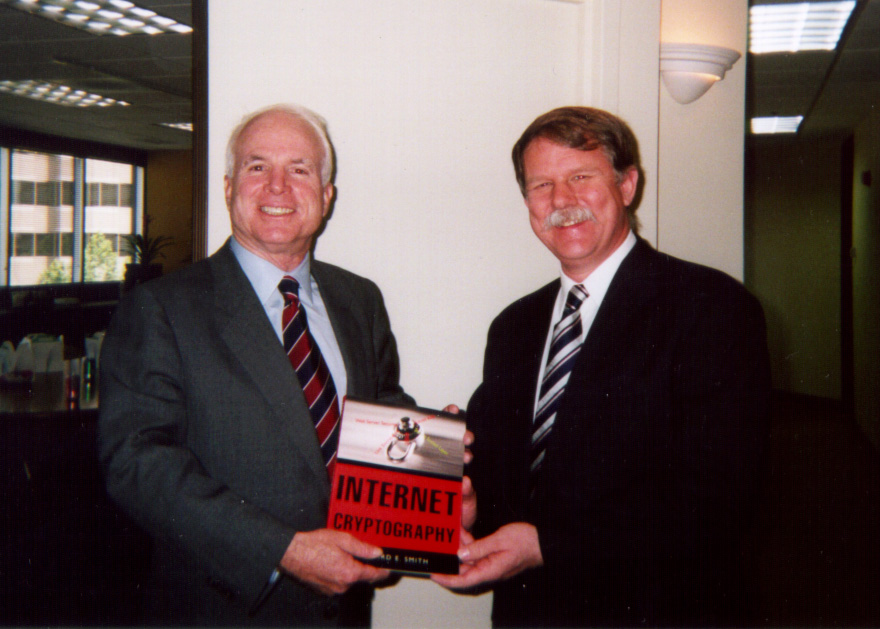
Sen. John McCain, 1936-2018
In June, 1999, Senator John McCain had started his presidential bid and was visiting companies in…
-
Interesting Email Scam I Received
I received an impressive email scam recently. My response was to forward it to the email…
-
How to Trace an Email Message
There is no way to verify an email’s contents except through cryptography. Until every email client…
-
HR and Phishing
I receive thousands of emails every month. I do a lot of (for me) critical activities…
-

The Six Types of Cyber-Risks
My textbook lists categories of cyber-attacks that focus on an attack’s lasting impact: how does it affect the…
-
Quantum Skepticism
Quantum computing gives us a way in theory to quickly crack certain types of cryptography. Well-funded…
-
The Big Bug in the News: the WPA2 flaw
The big news this week is a protocol flaw in the Wireless Protected Access protocol, version…
-
Comparing Leaks: Trump vs. Hillary
As I said in an earlier post, no crime is committed if the appropriate official leaks…
-
Tiptoeing Through Vulnerabilities
I sympathize with developers who throw up their hands and say, “I don’t do security stuff.”…
-
How DVD Crypto Keys Work
Here are a couple of short videos that describe the basic cryptographic mechanisms used in DVDs.…
-
Cryptosmith Video Series
The Cryptosmith video series uses animation to explain well-known crypto techniques. This should help more people…

You must be logged in to post a comment.