Rick
-
PDP 1s and Model Trains
Elsewhere on the Internet last week, people were solving a mystery about a PDP-1 running a…
-

Cities, Disneyland, and Software Security
I like to think of our modern software infrastructure as being like a large city and…
-

libhairshirt vs libfootgun
Peter Gutmann, an interesting crypto-academic from New Zealand, has proposed discussing two crypto libraries, libhairshirt and…
-
Cloud Security Specialization Launched
The University of Minnesota now offers a Cloud Security specialization through Coursera. It contains four courses…
-
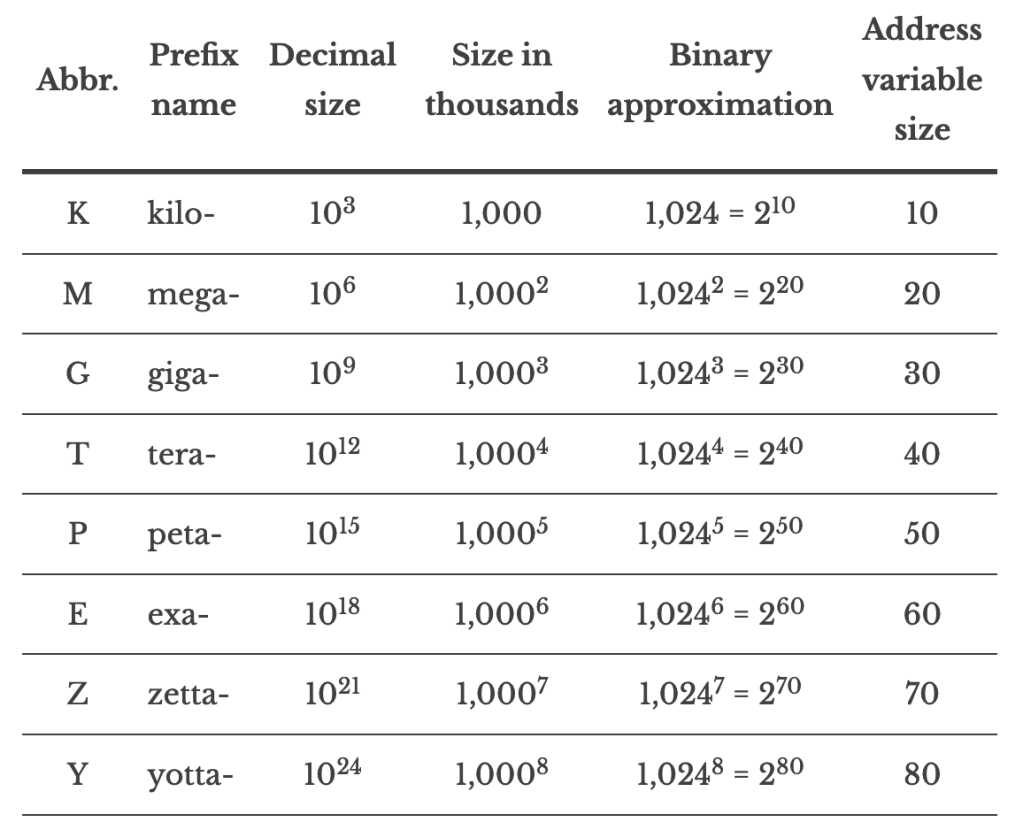
Memory Sizes: Now with zetta and yotta!
One of the most popular pages on this site provides a simple conversion to map numbers…
-
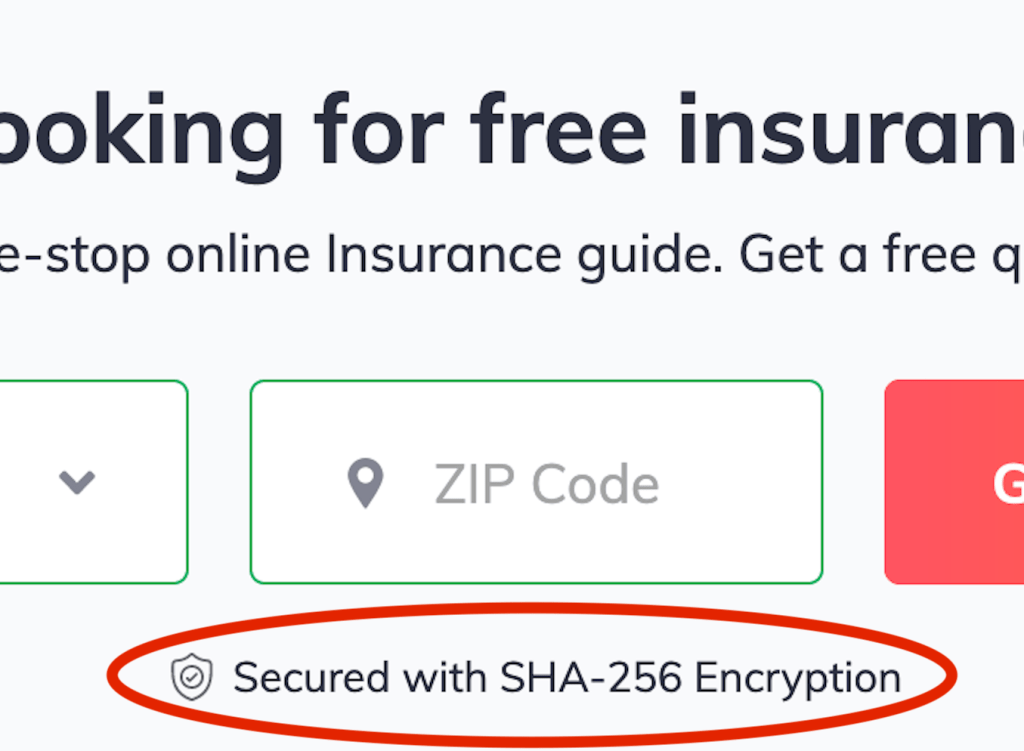
Selling It: Crypto Edition
Here is a crypto version of “Selling It,” a long-running back-page column in the magazine Consumer…
-

Old Story: Leaked Voter Records
My previous posting on the Proud Boys spam email speculated that voter records were widely available…
-

“Proud Boys” Emails Are Bogus
The Proud Boys emails aren’t actual threats. They’re the lowest form of anonymous spam.
-

2021 MSSE Cloud Security Elective
UPDATE: This elective will be offered to second-year MSSE students at the University of Minnesota as…
-

Krebs’ Three Rules
Like most people, I’m drawn to those small lists of “rules” that promise to make our…
-
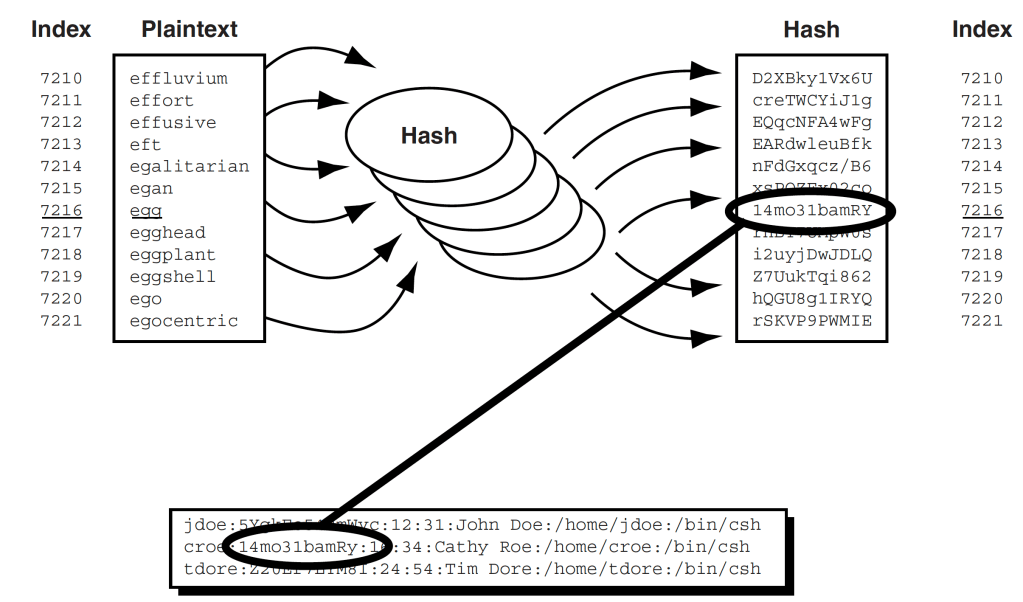
Basic Tech-y Article on Password Hacking
Here’s an article from last year’s Scientific American: The Mathematics of (Hacking) Passwords. If you remember…
-

Assessing an Email’s Legitimacy
I recently received an email sporting “Wells Fargo” logos. It asked me to do a survey.…
-
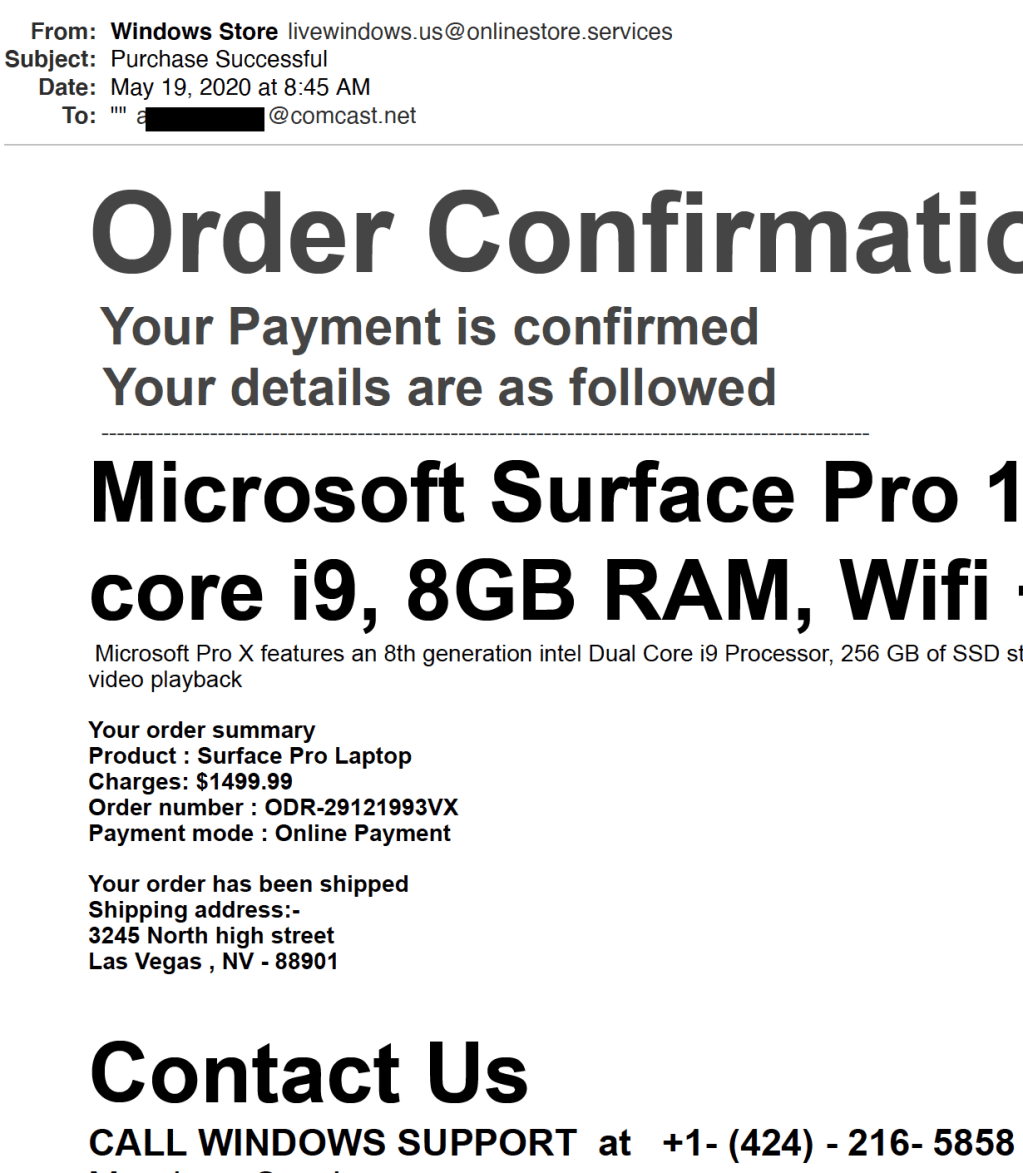
Beware of Phone Phishing
Just because the email (or letter) directs you to a phone number doesn’t mean you aren’t…
-

Solo Studio for Video Lectures
I’ve been recording video lectures for a Coursera specialization in cloud computing. The first of the…
-
FCPX and the Solo Studio
In other posts I describe how I’m producing videos for a Coursera specialization. This is a…
-

“Eyes Only” Revisited
I was poking around declassified documents from the National Reconnaissance Office (NRO) and found a reference…
-

Self-teaching a little security thinking
There’s a particular mindset we call security thinking. I’ve also seen it called ‘reasoned paranoia.’ The…
-

About …
Cryptosmith Institute is a retirement-time enterprise of Dr. Rick Smith, author of Elementary Information Security (Jones and…
-
Detecting a Phish on an iPhone
In their obsession with simplifying the phone interface, the iPhone designers make it a bit harder…
-
Online Course in Cloud Security Basics
I now offer an online course on Cloud Security Basics under the auspices of the University…
-
Life Cycle of a Security Bug
Unlike members of the insect family, computer software bugs live forever. Software security bugs (well, flaws)…
-
“Eyes Only” Security Marking
[This post has been UPDATED three times since first published, most recently on Nov 14, 2019]…
-
WPA2 Packet Frame Format
Wireless Protected Access, Version 2 (WPA2) is the version of Wi-Fi security used in most cases…
-
Ethics and Chatbots
I was online chatting at a web site to repair my lawn tractor. Once I finished,…

You must be logged in to post a comment.