Rick
-
Towards a practical digital library
I started collecting digital content in the 1980s. Before that I was satisfied to print things…
-
My invitated – a classic phishing attack
Phishing emails can be tiresome. Sometimes, though, they are classically bad. Even better, this one uses…
-
Migration Round Trip
A few weeks from now I’ll throw the switch and redirect Cryptosmith web traffic to its…
-
The Migrating Web Site
I am moving my Cryptosmith web site to WordPress.com. This will give me a lot more…
-
John Oliver on Net Neutrality
Comedian John Oliver has recorded a classic rant about net neutrality. Here’s my favorite quote: The…
-
The “Bug-Free Software” fallacy
About 20 years ago, I worked with a fellow who proudly told me that he had…
-
Multics was flawless?
Last week I participated in a very geeky panel discussion about a now-defunct standard for computer…
-
Example of KISS
Ok, this is a backwards observation. One of my hot buttons is to spot “cyber security…
-
Digital’s RT-11 File System
(Circa 1975-199?) The PDP-11 computer, build by Digital Equipment Corporation (DEC) in the late 20th century,…
-

Security Design Principles
This is an extended, less-edited version of an article appearing in IEEE Security and Privacy in December 2012. This…
-
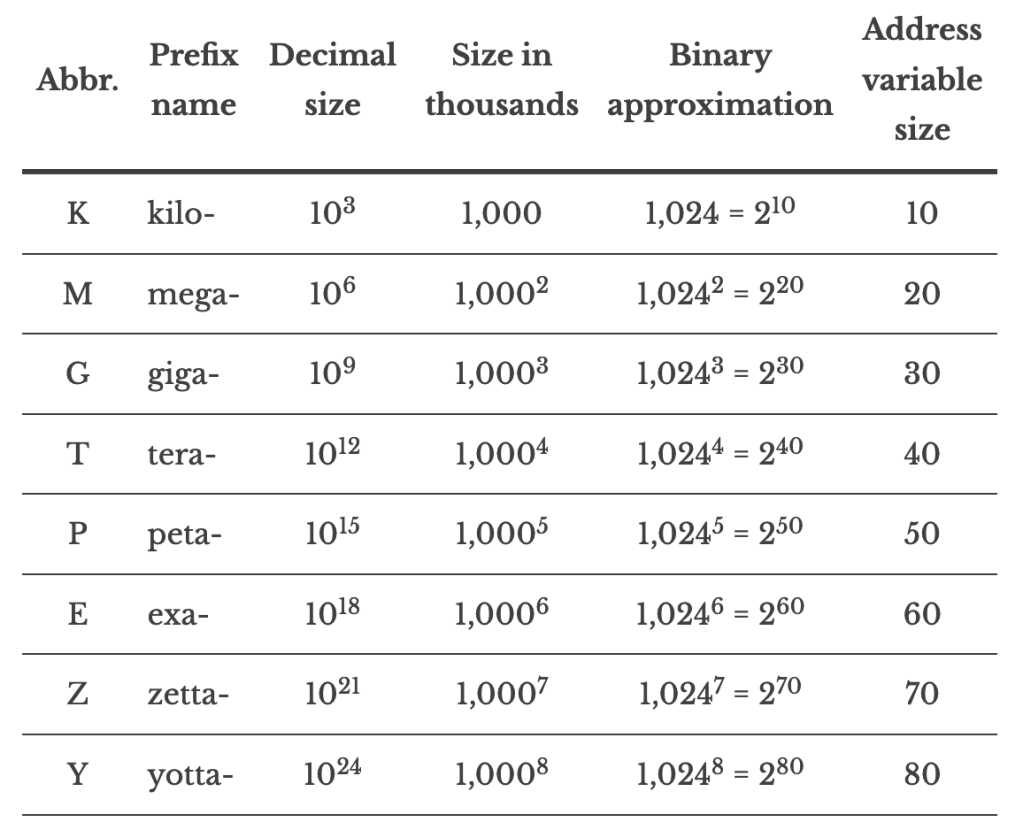
Kilo mega giga tera
I am not keeping this page up to date. Please visit https://cryptosmith.com/2013/10/18/memory-sizes-kilo-mega-giga-tera-peta-exa/ instead. Here is a…
-
Memory Sizes: kilo mega giga tera peta exa
Here is a table summarizing large numbers, their names, and the number of bits they require…
-
GUIs: Control, Conveyance, Continuity, and Context
I’m a sucker for basic principles distilled into pithy prescriptions. A freelance writer, Brian Boyko, has…
-
A really simple Drupal 7 example module
I developed this module back when I managed my self-hosted Drupal system. Since then I’ve found…
-
Boston University’s RAX Library
(circa 1973-8) Boston University (BU) developed its own timesharing system in the 1970s for its IBM 360…
-
Homework
LakesideMap
-
Pragmatic Security: the history of the Visa card
I’ve been looking at the evolution of electronic funds transfer (EFT) and payment systems recently. My…
-
Boak’s Puzzle: Disposing of Classified Trash
Recently I was skimming through the NSA’s “classified history of COMSEC” (Volume 1 and Volume 2). This…
-
Real-world document encryption
I’ve been reviewing histories of cryptography recently and here’s an interesting thing about pre-computer encryption: it’s…
-
Design Patterns for Identity Systems
These are design patterns in the Christopher Alexander sense rather than the object oriented design sense:…
-
A Simple CPU Demonstration
CPU = Central Processing Unit The CPU is the working part of the computer. It runs your…
-
Fixing the Insider Threat: Separation of Duty
The insider threat isn’t easy to fix. We can fix it with Separation of Duty, but…
-
Files using Classic FORTH
(circa 1970-85, maybe later) The Forth programming system was developed in the late 1960s by Chuck Moore.…

You must be logged in to post a comment.