Rick
-

Teaching with Design Principles
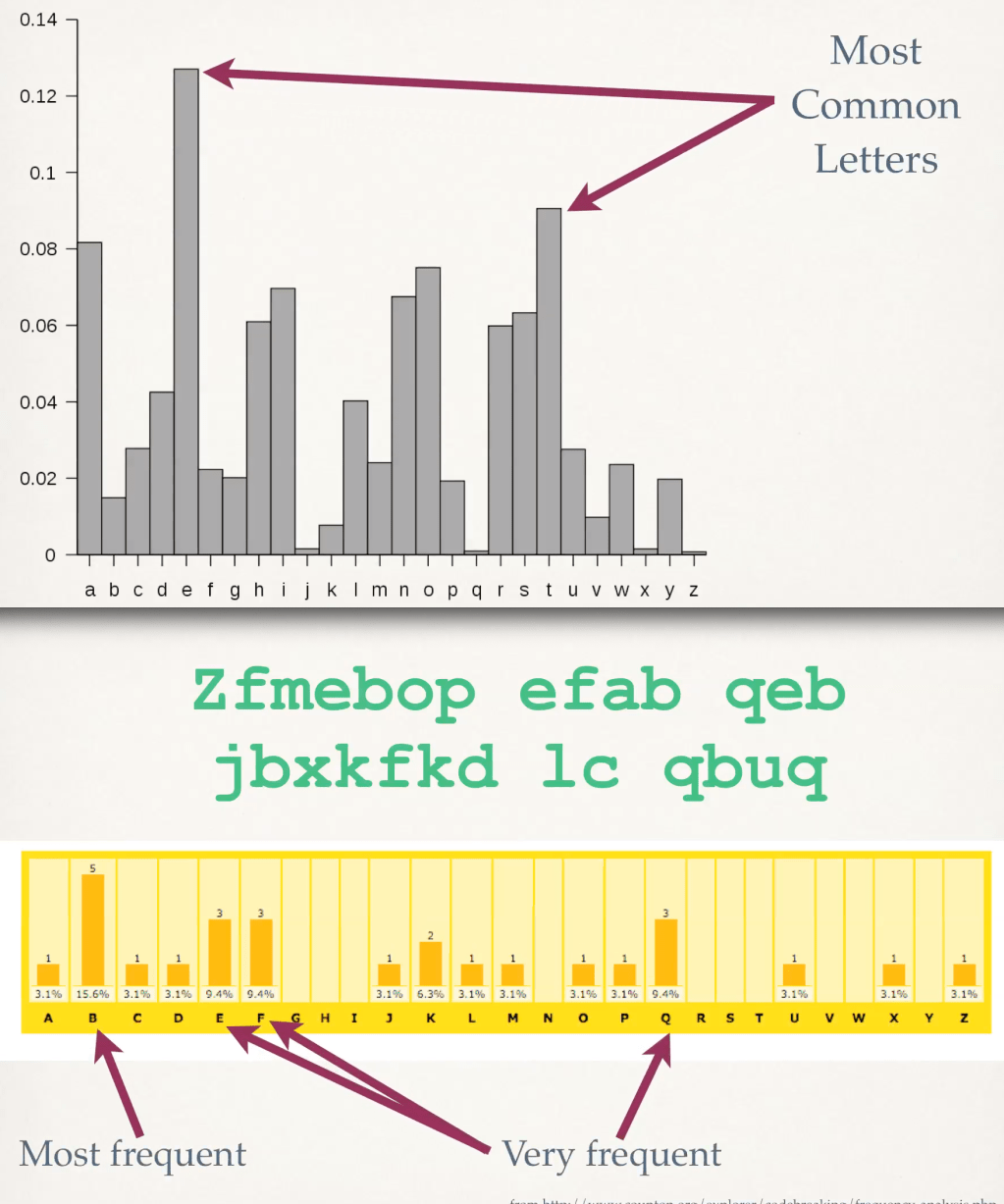
Design principles help students learn the essentials of technical design tasks. Students apply simple-sounding rules to…
-
Why Signalgate Matters
I found this in my files. I no doubt intended to publish it months ago and…
-

Another Telephone Phish
A person called me on the phone a few moments ago claiming to be from US…
-
Making Fun of Quantum Codebreaking
Quantum codebreaking uses a theoretically “large” quantum computer to break secret codes. Today, quantum computers handle…
-

War Plan Chat Includes Journalist
Journalists aren’t usually invited to online chats about US war plans. This seemed obvious until yesterday,…
-
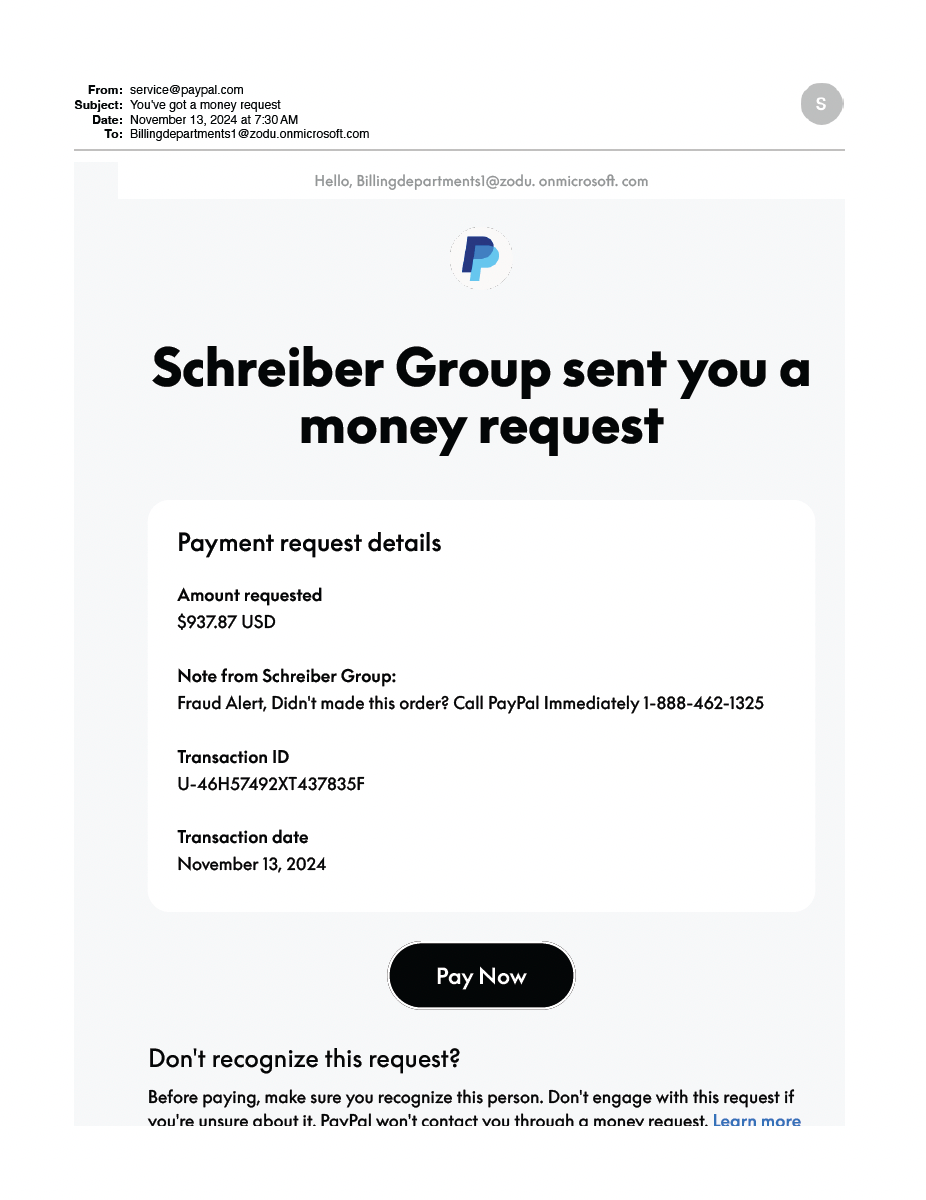
Clever PayPal-based Attack
Do not call that number! This attack is brilliant. It uses a legitimate PayPal email message…
-
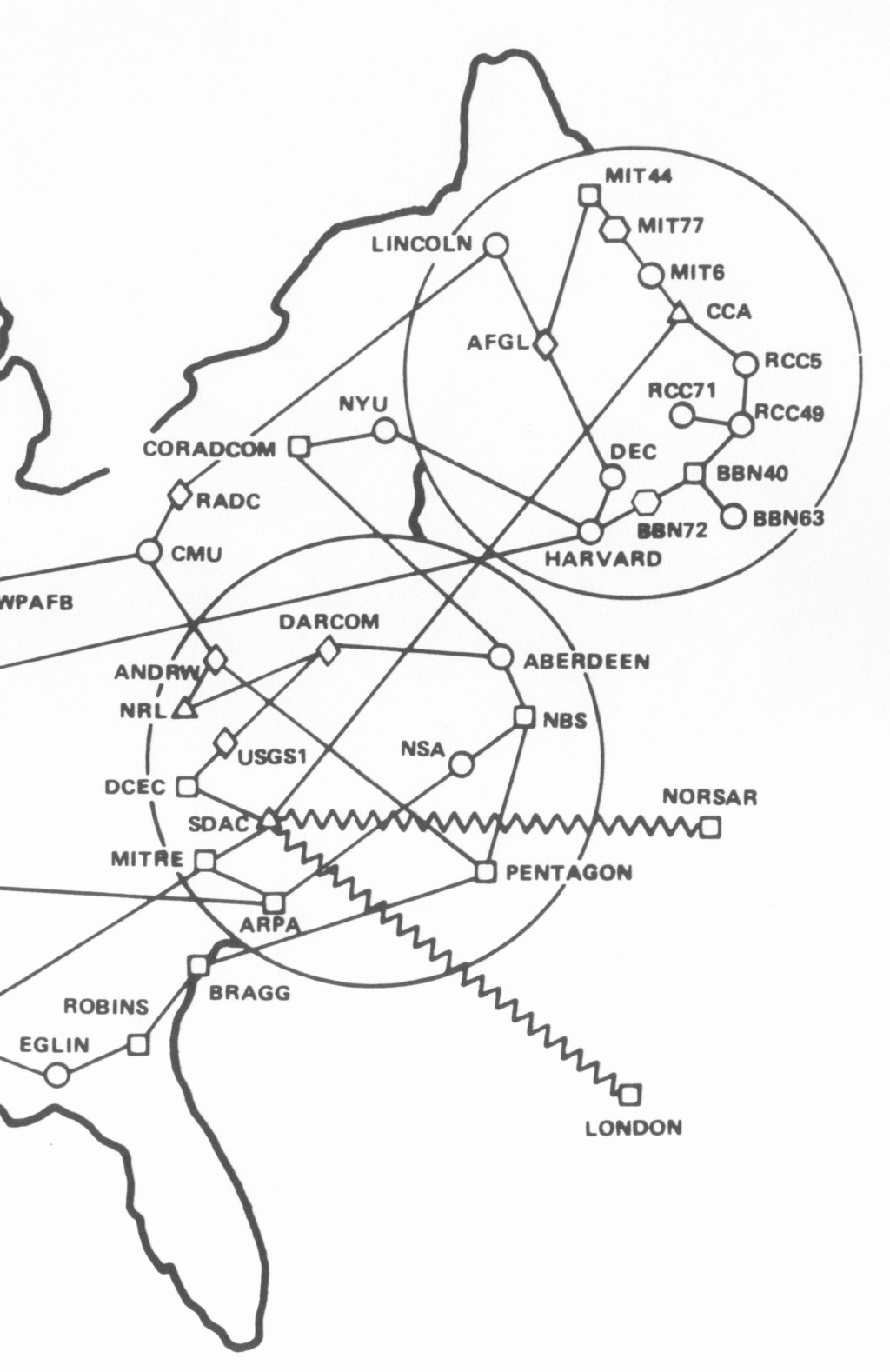
ARPANET Maps
Here is a set of geographical maps of the ARPANET in the 1970s and 1980s. There…
-

Breaking Bitlocker
It was only a matter of time before someone did this. Bitlocker is Microsoft’s technique for…
-

Play the Password Game!
A clever person has hosted a Password Game. Give it a try!
-

Leaking Secrets Under Social Pressure
Here is a classic example of human nature: people on a gaming site argue that the…
-

GPT and Confirmation Bias
“Garbage in, garbage out.” In computing we’ve recited the GIGO motto since I was in diapers…
-

SCI//HCS-P/SI/TK at Mar-a-Lago
This is a brief explanation of the weird acronyms on the cover sheets that appeared in…
-

The Mar-a-Lago Mess
Update: Former President Trump has been indicted under federal laws for unlawfully retaining government documents and…
-
The Quantum Computer Bogeyman
Peter Gutmann of the University of Aukland recently published a parable “On the Heffalump Threat.” He…
-
Can I auto-post to Mastodon?
Update: My autoposting mechanism never really worked. Fortunately, WordPress.com developed an autopost mechanism that I can…
-

Mastodon
Like lots of other people, I’m looking at Mastodon as a newer, better tech-social community. I’m…
-

Writing Nonfiction with ADHD
[Revised 17 Dec 22] This post is inspired by Tessa Flattum’s post, “How to Write a…
-
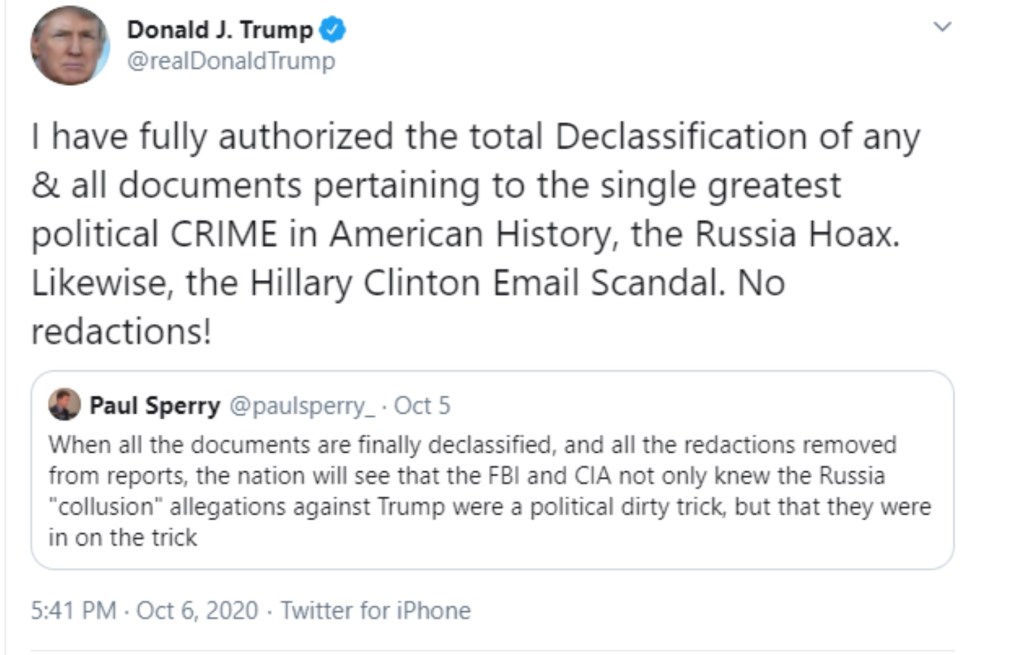
Telepathic Declassification
Former President Trump recently suggested that the sitting President simply needs to “think” something is declassified…
-

Email Attack via a Recycled Domain
A software engineering friend fell victim to an almost-successful attack on his Facebook account. The attacker…
-

Cybersecurity for MSSE 2023
MSSE second-year students may request a cybersecurity elective as course SENG 5271. If the course is…
-
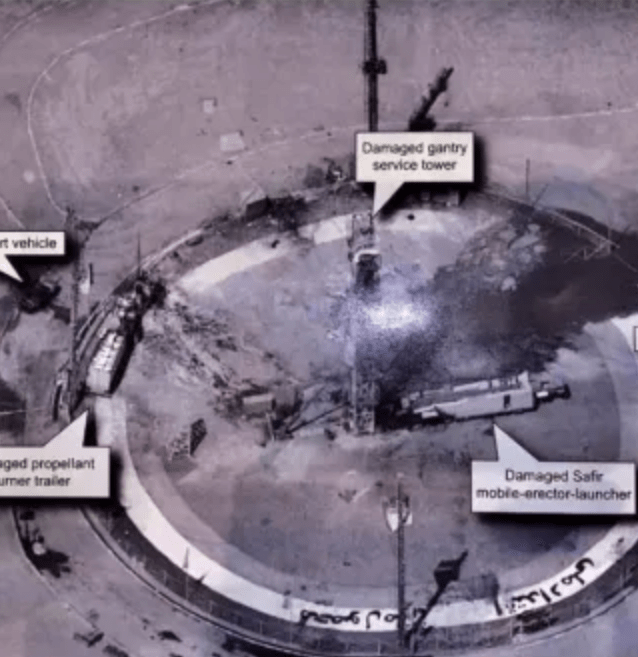
Update: Tweeting Top Secret
Back in the dark ages of the Trump presidency, the President tweeted this photograph. An earlier…
-
Online Course: Cloud Top Ten Risks
I am pleased to report that the fourth course for the University of Minnesota in my…
-

Cybersecurity for MSSE 2022
I am offering an online cybersecurity elective to MSSE second-year students for 2022: SENG 5271. It…

